USE CASE
Simplified Compliance and Auditing
Account and access management processes that are by design demonstrably compliant with relevant information security and privacy guidelines.

CHALLENGE
How to Ensure Demonstrable Compliance in a Complex, Dynamic It Landscape
In organisations that sometimes have hundreds or thousands of different users, working with dozens of applications and data sources, managing individual user accounts and access rights is a complex task. How can we address this so that the organisation is not only certain of its compliance with current information security guidelines, but can also easily demonstrate that compliance?
NECESSITIES
Features
HOW IT WORKS
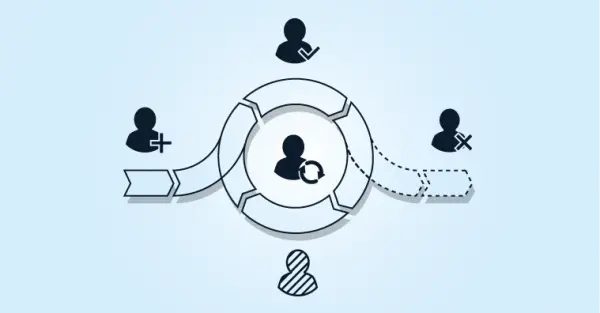
How We Establish a Compliant and Auditable Identity and Access Management System
7 steps that can each be configured using low-code or no-code solutions
Source system: Integration of HelloID with source systems such as HR, SIS and/or scheduling systems. This way, changes in the source data are automatically available in HelloID.
People: Conversion of data about people/roles from source systems to a common representation within HelloID using an ‘identity vault’.
Business rules: Determining rules that determine which roles are granted which types of accounts and access rights, and under what conditions.
Target systems: Linking HelloID to on-premises and/or cloud-based applications. This can be executed step by step per application.
Service processes: Automating processes, including online approval flows and activation in target systems. This can be carried out step by step for each process.
Access management: Set up access procedures, such as Single Sign-On (SSO) and Multi-Factor Authentication (MFA), in conjunction with — for example — Active Directory.
Reporting and auditing: Configuring standard and client-specific reports and monitoring functions for analysis and audits.